Establishing digitally sourced trusted identities is not only critical to fighting money laundering by reducing risk, it will also improve the customer experience and save companies significant resources.
Identification is based on the resolution of the identity of a person using trusted, reliable sources of information to achieve confidence not only that the person exists, but also to authenticate that the individual is the person to whom the identification belongs. The strength of the identification process directly contributes to the integrity of information, which is used to untangle potential proceeds of crime from legitimate property.
Anti-money laundering (AML) professionals need an approach to assess the strength of identification and how to apply reasonable measures to reduce risk to execute on a risk-based program to fight money laundering. The Association of Certified Anti-Money Laundering Specialists (ACAMS) white paper “Digital Identification Methods Testing and AML Programs”1 presents a case study approach to help audit and compliance personnel keep pace with the various identification innovations methods and how to test each one based on their designs.
The Role of Identity Within Programs Built to Combat Proceeds of Crime and Their Challenges
Identifying the persons who own or control property held by financial institutions (FIs) and participating organizations within an AML regime has always been a core component of know your customer (KYC) data collection. Recognizing this, Recommendation 10 of the Financial Action Task Force (FATF) includes identification in KYC collection. However, executing identification varies from the principles-based approach of achieving a “reasonable belief that it knows the true identity of each customer” in the U.S. to more prescribed methods in other countries.
Onboarding and subsequent processes typically rely on identification documents and other records provided by the customer to the FI, which can run the risk of being fraudulent. The review of photo identification documents by staff can fail due to inexperience with the type of records, a resistance to challenging a customer for fear of loss of business or internal compromise of the employees. Masking identities with pseudonyms or synthetic identities are methods used by criminals to obscure the connection to proceeds of crime.
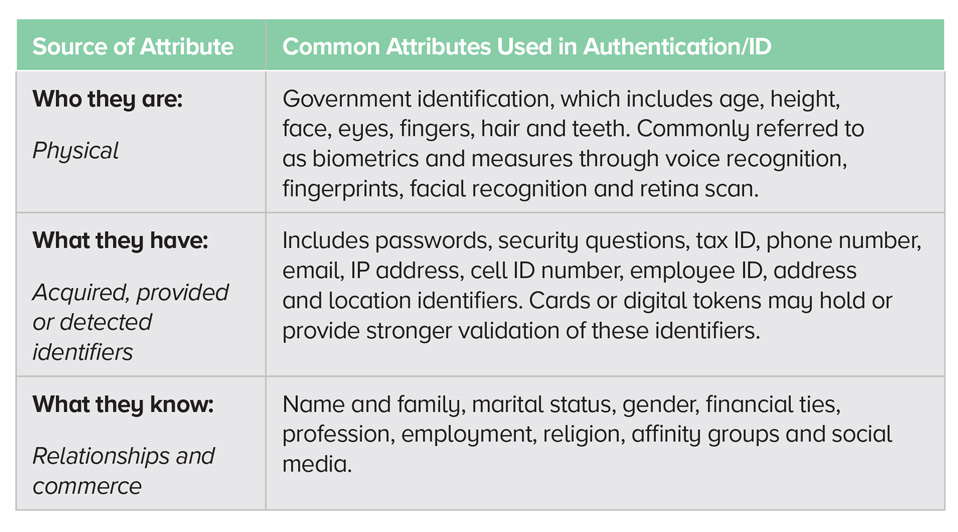
To strengthen the security of communications with customers, FIs often request more information from customers to build makeshift supplementary passwords. This includes customers’ answers to historical or personal questions as a tool when enhanced authentication was later needed to authorize higher-risk transactions or account changes. However, due to social media, many of these private details have entered the public domain, and this method has had a dramatic reduction in its effectiveness.
A common challenge when relying on physical records is addressing fraud risk by confirming that a record is valid when it has been provided by the client. Within digital networks, this is solved with the client’s authorization to share a record from one network provider to another participant network and have the authentic record delivered in a timely manner.
Enhanced authentication over digital networks uses multifactor authentication. Multiple forms of communication (e.g., phone call, text, mail, conversation) are used to confirm that the person has control of more than one communication channel as provided during the identification stage.
Why digital identification now? The Pivotal Point in the Evolution of Identification
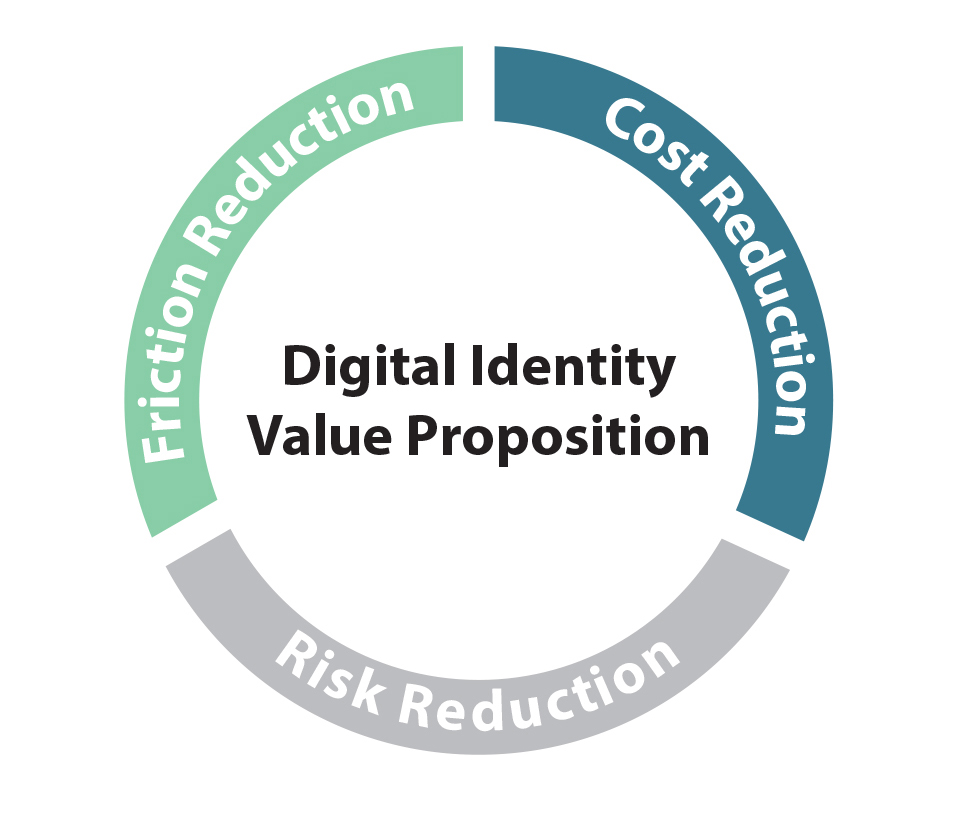
Innovations in identity management, such as moving from physical to authenticated electronic records, improve record integrity (reduce risk), are more efficient due to reduction in staff time to review documents (reduce cost) and are easier for the customer through online access (reduce friction).
Commercial solutions that create digital identity networks managed by the person and using trusted stewards of data, known as self-sovereign identity, also evolved. Technology has strengthened identity-access management of systems into robust processes involving cryptography to provide reliable and traceable tools for confirming the legitimacy of information exchange to a source. These new tools have resulted in frameworks that can provide identity solutions for commerce that are comparable or stronger than in-person methods, while adding significant efficiencies for global trade.
Government approaches to embracing technological changes have varied with some methods turning to enhancing national-identity-document programs with biometrics and additional data, while others have turned to trust frameworks and digital identity tokens.
In response, FATF has released digital identification guidance with a target date of February 2020. The FATF Digital Identification Guidance version released for consultation on October 31, 2019, has raised the opportunity for countries to adopt an AML risk-based approach in relation to identification assurance. Principles-based guidance can help steer international approaches in accepting identity across borders, aid in financial inclusion and support the sharing of innovations to both reduce friction for consumers and fight crime.
Defining Identification—Answering the Question, “Who are you?”
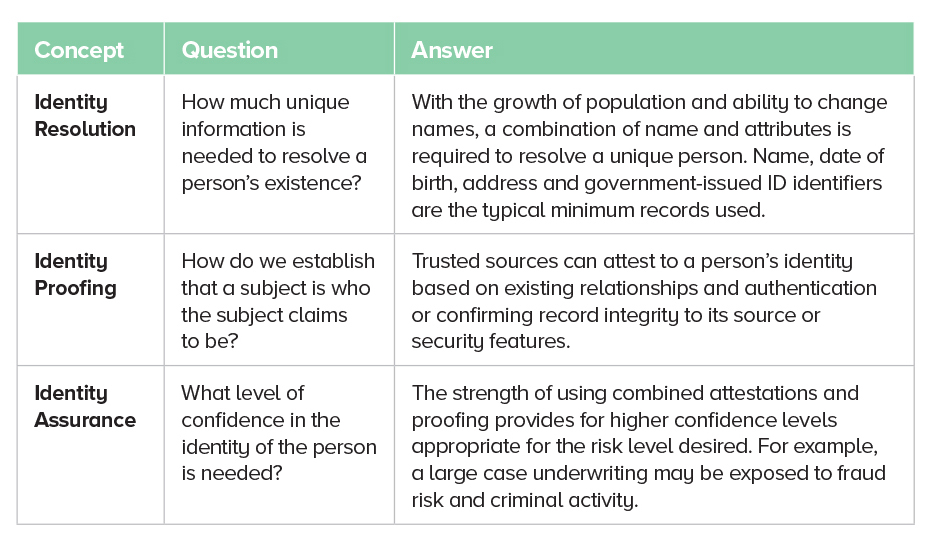
Identification is the process of establishing the resolution of a unique person (either individual or entity) through the use of attributes provided by a reliable source (i.e., based on trusted record[s] or organization[s]), and matching them to a person (identity proofing). However, in order to comply with AML programs, the traceability of the identification is a critical part of compliance.
Understanding Identity Concepts to Assess Identification
These concepts are more thoroughly explained and defined in international standards, such as the National Institute of Standards and Technology’s “Digital Identity Guidelines”2 for the U.S., which are used by both the public and private sector. For the European Union (EU), it is the electronic Identification Authentication and Trust Services regulation, which requires cross-acceptance across the European Union,3 and for the United Kingdom, it is on gov.verify,4 which is a public-sector led network with active private-sector participants.
The three concepts in the table below will help determine the strength of an identification process.
Each one of them has a relationship with both the authenticity and the reliably source(s) of records.
Authentication—Answering the Question: “Is it you?”
For existing relationships, to gain the authorization to access an account, a consumer will need to provide attributes to confirm that the consumer is the person who has the relationship with the FI.
Enhanced authentication or an update of the identification has shown to be critical to
reduce the residual risk of fraud for both nonfinancial (address changes) as well as high
valued financial transactions (unauthorized withdrawals).
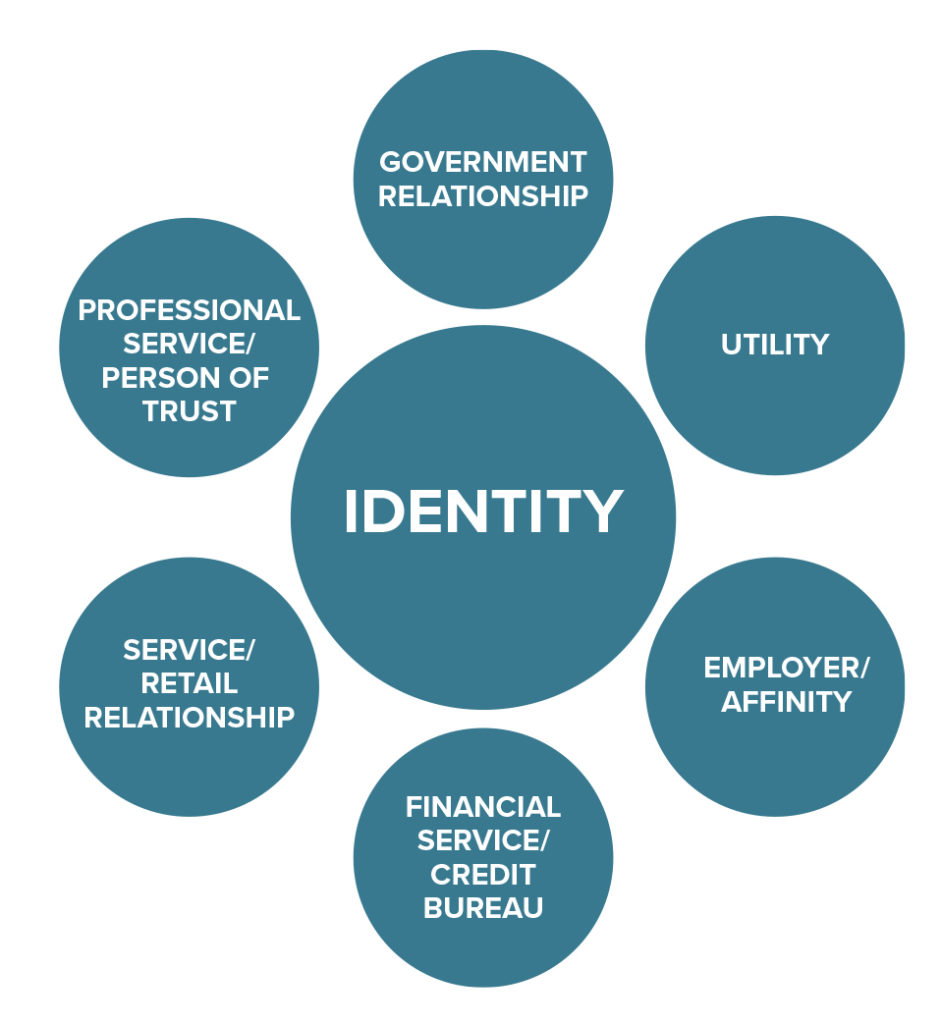
Reliable Sources of Identification
A reliable source of identification information, whether it be a government body, an organization or a person, should have the following features:
- Support an ongoing relationship and not a one-time service
- Be in a sector that requires strong record-keeping practices and controls for all stages of a customer’s life cycle
- Have an active and sustained relationship with the person being identified
- Provide traceability and reliability
- Provide security features to support the authenticity of the record
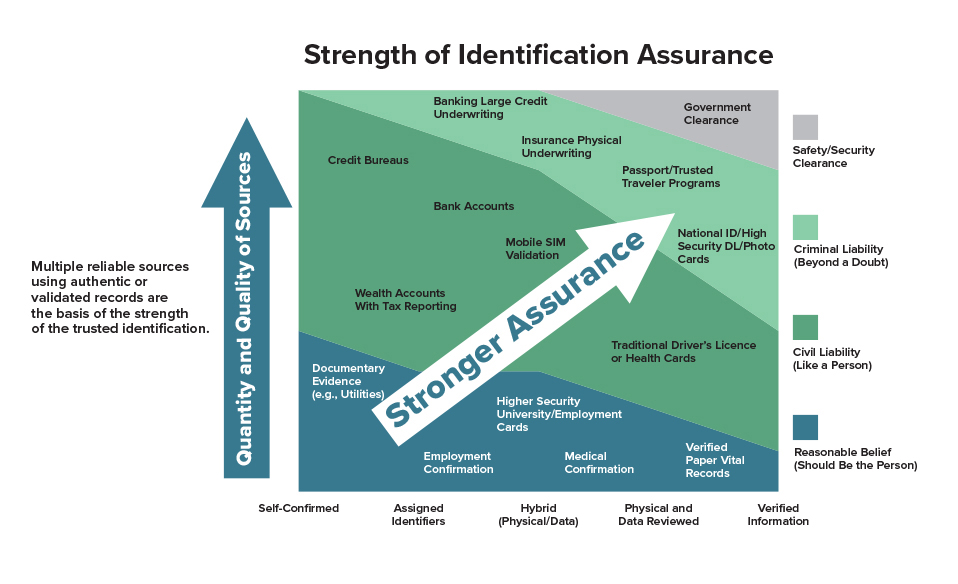
The above graphic displays the relationship with the attestation of reliable sources compared to the proof level of the attributes used in an identification process to achieve levels of identity assurance and overall reliability.
For example, government clearance would require both multiple attestations (confirmation of relationships using background checks) as well as a high-proof level (through the validation of records to their sources) for the clearance to be granted.
By using multiple records that have a high degree of authenticity with historical and physical presence confirmation the confidence and assurance of a person being both unique and existing could be reasonable
By using multiple records that have a high degree of authenticity with historical and physical presence confirmation, the confidence and assurance of a person being both unique and existing could be reasonable. This method to use additive records with varying strength of resolution of a person confirms that stronger levels of assurance can reasonably be established with a few degrees of separation from government-sourced identification within a risk-based approach.
Recommendations and Factors to Consider
- FIs should assess their identification strategy to determine which method(s) meet their needs and those of their customers.
- Identification at onboarding and triggers to refresh based on the risk of the customer and their transactions
- Privacy and information security risk factors in collecting and managing the information
- The type of information that needs to be verified (income, employment, age, medical, tax residency, banking, communications, etc.)
- Having a higher level of identity assurance, reducing fraud risk and improving knowledge of customers can be attained by the following:
- Increasing the number and reliability of sources of information
- Verifying the attributes to the sources of information (match)
- Including identity attributes in monitoring and analytics programs by maintaining traceable records
- Considering, monitoring and testing all identification methods for pros and cons
In conclusion, leveraging the strength of digital identification methods to improve the integrity of information is a powerful tool to untangle proceeds of crime from legitimate property.
- Eugenio (Gene) DiMira, “Digital Identification Methods and Testing for AML Programs,” Association of Certified Anti-Money Laundering Specialists, https://www.acamstoday.org/wp-content/uploads/2021/03/DiMira-Digital-ID-Define-Test-Whitepaper.pdf
- Paul A. Grassi, Michael E. Garcia and James L. Fenton, “Digital Identity Guidelines,” National Institute of Standards and Technology, https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-63-3.pdf
- “Trust Services and Electronic identification (eID),” European Commission, https://ec.europa.eu/digital-single-market/en/trust-services-and-eid
- “Guidance Gov.UK Verify,” GOV.UK., https://www.gov.uk/government/publications/introducing-govuk-verify/introducing-govuk-verify. Verify allows partner companies to verify the identity of the person for ongoing access to online services.